Certified Information Security Manager CISM Training
Certified Information Security Manager CISM Training
Training Certified Information Security Manager CISM - Online E-Learning Training. Order and start immediately for the best price.
Read more- Brand:
- ISACA
- Discounts:
-
- Buy 2 for €351,82 each and save 2%
- Buy 3 for €348,23 each and save 3%
- Buy 4 for €344,64 each and save 4%
- Buy 5 for €341,05 each and save 5%
- Buy 10 for €323,10 each and save 10%
- Buy 25 for €305,15 each and save 15%
- Buy 50 for €287,20 each and save 20%
- Availability:
- In stock
- Delivery time:
- Ordered before 5 p.m.! Start today.
- Award Winning E-learning
- Lowest price guarantee
- Personalized service by our expert team
- Pay safely online or by invoice
- Order and start within 24 hours
Certified Information Security Manager CISM E-Learning Training
Gain the expertise to manage, design, oversee, and assess enterprise information security — while preparing for the globally recognized CISM certification.
The Certified Information Security Manager (CISM) course is designed for professionals who are responsible for managing, designing, supervising, and evaluating an organization’s information security function.
This training is ideal for experienced security managers, consultants, and IT auditors looking to enhance their strategic and policy-level skills in information security management.
Requirements:
A minimum of five (5) years of experience in information security management.
Experience waivers are available for up to two (2) years, depending on your qualifications.
ISACA® Certified
E-learning course (21+ hours) – includes interactive modules, official practice exams, and guidance from an online mentor.
Course content
CISM 2022: Information Security Governance
Course: 1 Hour, 40 Minutes
- Course Overview
- Business Model for Information Security (BMIS)
- Asset Identification and Classification
- Supply Chain Security
- Personnel Management
- Information Security Programs
- Reviewing Service-level Agreements (SLAs)
- Change Management
- Configuration Management
- Organizational Security Policies
- IT Maturity Models
- Capital Versus Operating Expenses
- Chain of Custody
- Organizational Culture and Security
- Use of Control Objectives for Information Technologies (COBIT) for IT Governance
- Course Summary
CISM 2022: Business Continuity & Security
Course: 1 Hour, 13 Minutes
- Course Overview
- Business Continuity Plan (BCP) and Business Impact Analysis (BIA)
- Disaster Recovery Plan (DRP)
- Data Roles
- IT Security Roles
- Contractual Obligations
- Security Baselines
- Establishing a Performance Baseline on Windows Server
- Establishing a Performance Baseline in the Azure Cloud
- Physical Security
- Security Control Types
- Course Summary
CISM 2022: Incident Response
Course: 42 Minutes
- Course Overview
- Incident Response Plan (IRP)
- Incident Escalation
- Incident Eradication
- Incident Containment
- Post-incident Lessons Learned
- Automating Incident Response in the Cloud
- Course Summary
CISM 2022: Security Standards
Course: 53 Minutes
- Course Overview
- The European Union's General Data Protection Regulation (GDPR)
- ISO/IEC Standards
- America's Health Insurance Portability and Accountability Act (HIPAA)
- America's Federal Risk and Authorization Management Program (FedRamp)
- Payment Card Industry Data Security Standard (PCI DSS)
- Canada's Personal Information Protection and Electronic Documents Act (PIPEDA)
- China's Personal Information Protection Law (PIPL)
- Using the Cloud Controls Matrix (CCM)
- Course Summary
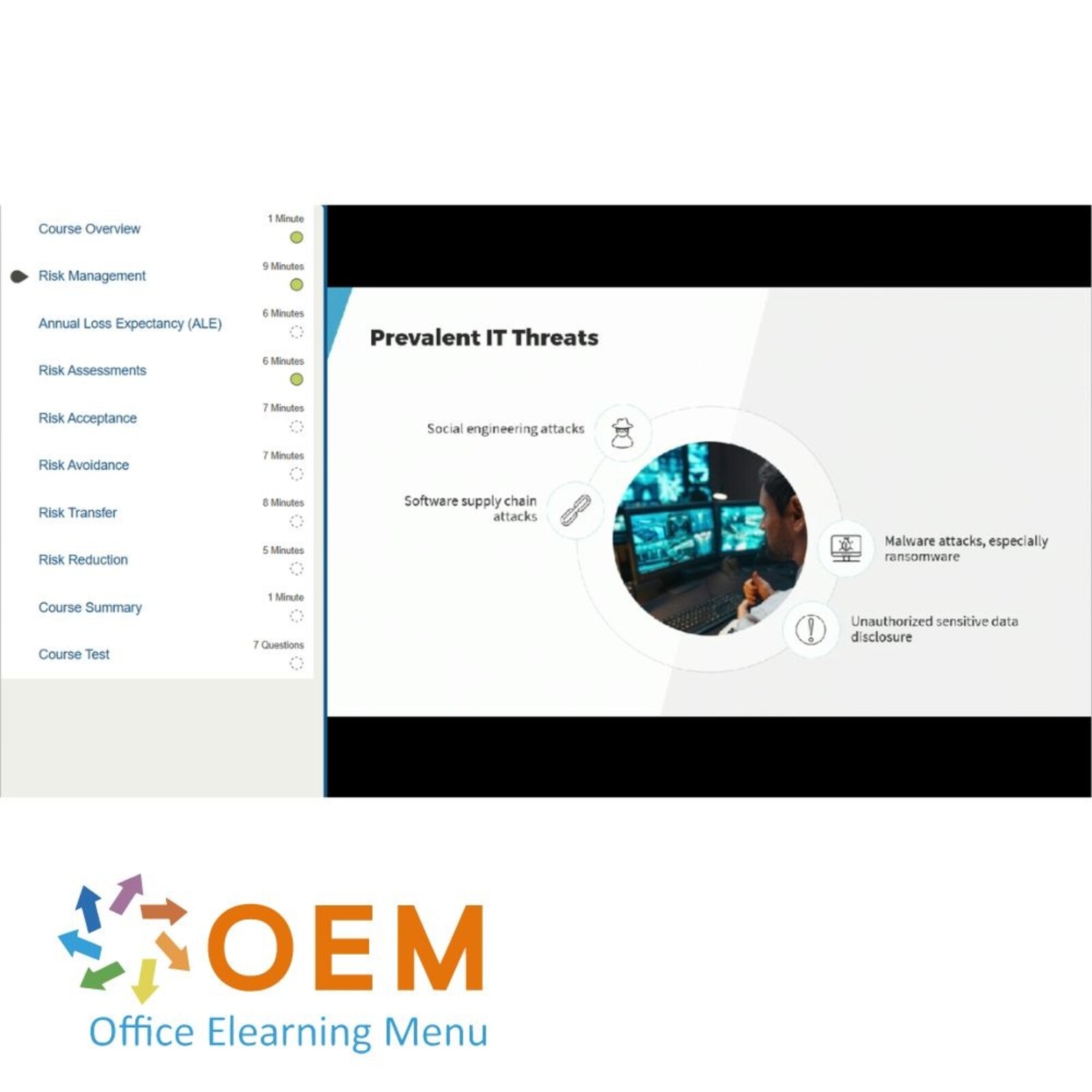
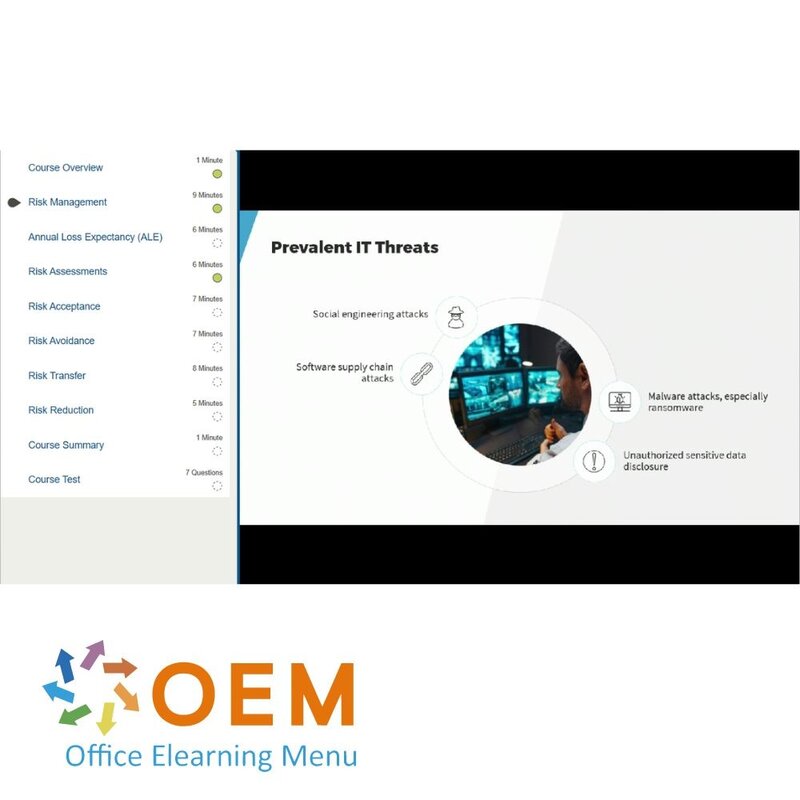
CISM 2022: Managing Risk
Course: 50 Minutes
- Course Overview
- Risk Management
- Annual Loss Expectancy (ALE)
- Risk Assessments
- Risk Acceptance
- Risk Avoidance
- Risk Transfer
- Risk Reduction
- Course Summary
CISM 2022: Data Privacy
Course: 57 Minutes
- Course Overview
- Personally Identifiable Information (PII)
- Data Residency
- Data Loss Prevention (DLP)
- Classifying Data with Amazon Macie
- Classifying Data with Microsoft Purview Governance
- Configuring Windows Server Data Classification
- Using Tags to Organize Cloud Resources
- Encrypting Cloud Storage
- Course Summary
CISM 2022: Assessing Risk
Course: 46 Minutes
- Course Overview
- Vulnerability Assessments
- Conducting a Network Vulnerability Assessment
- Scanning a Web Application For Vulnerabilities
- Perform a Gap Analysis
- Penetration Testing
- Viewing Cloud Resource Security Compliance
- Course Summary
CISM 2022: Managing Authentication
Course: 54 Minutes
- Course Overview
- Authentication
- Managing Amazon Web Services Users and Groups
- Managing Microsoft Azure Users and Groups
- Managing Linux Users and Groups
- Managing Windows Server Users and Groups
- Enabling Amazon Web Services IAM User MFA
- Managing Password Policies
- Identity Federation
- Course Summary
CISM 2022: Implementing Access Control
Course: 1 Hour, 2 Minutes
- Course Overview
- Authorization
- Access Control Models
- Configuring Windows Dynamic Access Control
- Administering ABAC through Azure Dynamic Groups
- Using Azure Permissions through RBAC
- Managing Windows File System Permissions
- Handling Linux File System Permissions
- Configuring Windows File System Auditing
- Using Active Directory Delegated Administration
- Course Summary
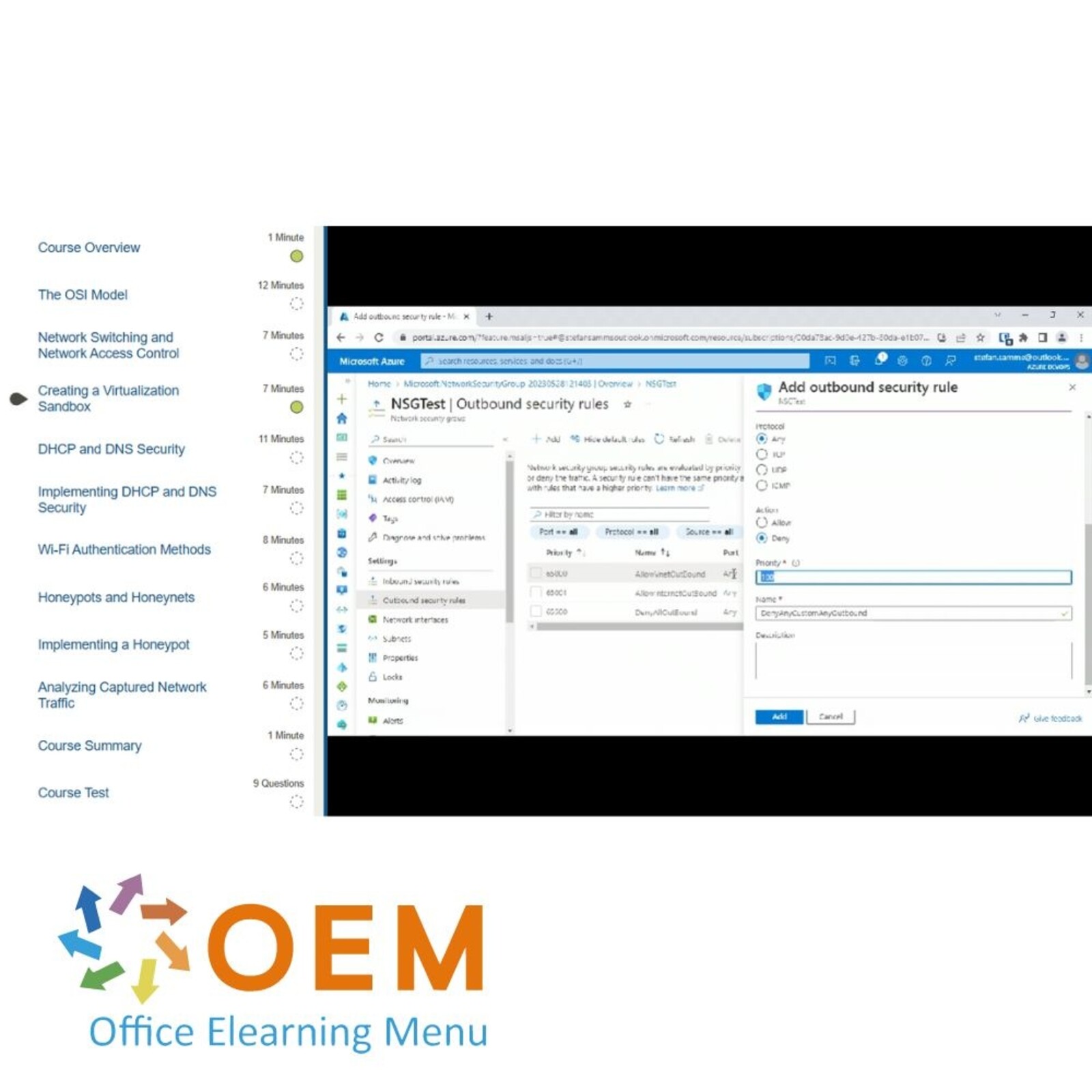
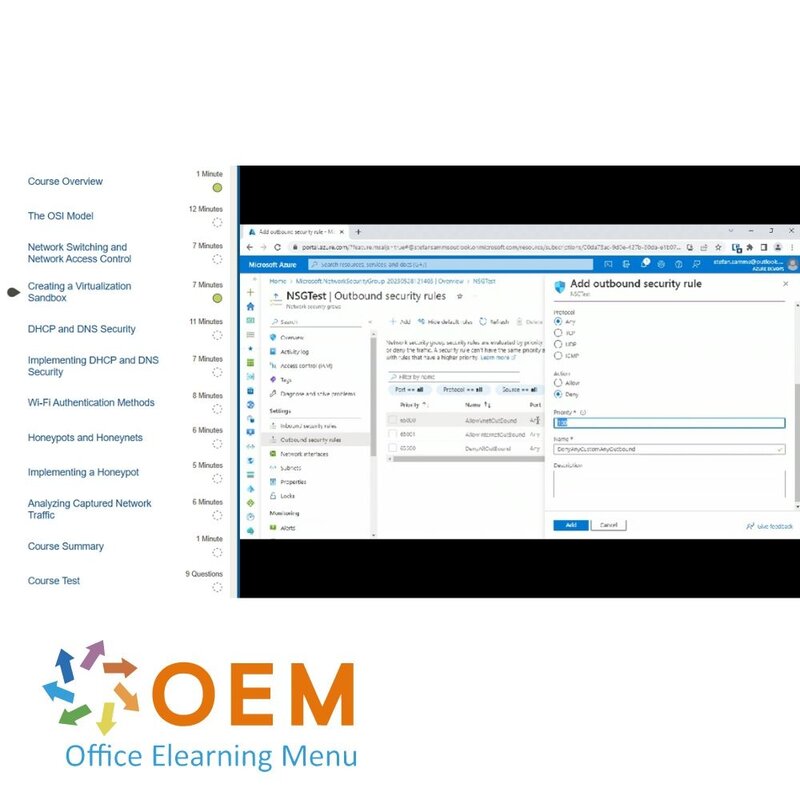
CISM 2022: Network Security
Course: 1 Hour, 11 Minutes
- Course Overview
- The OSI Model
- Network Switching and Network Access Control
- Creating a Virtualization Sandbox
- DHCP and DNS Security
- Implementing DHCP and DNS Security
- Wi-Fi Authentication Methods
- Honeypots and Honeynets
- Implementing a Honeypot
- Analyzing Captured Network Traffic
- Course Summary
CISM 2022: Network Attack Mitigation
Course: 1 Hour, 2 Minutes
- Course Overview
- Firewall Types
- Configuring Windows Defender Firewall
- Adjusting a Linux Firewall
- Manage Azure Network Security Groups (NSGs)
- Administering Microsoft Azure Firewall
- Proxy Servers
- Intrusion Detection and Prevention
- Configuring the Snort IDS Tool
- Course Summary
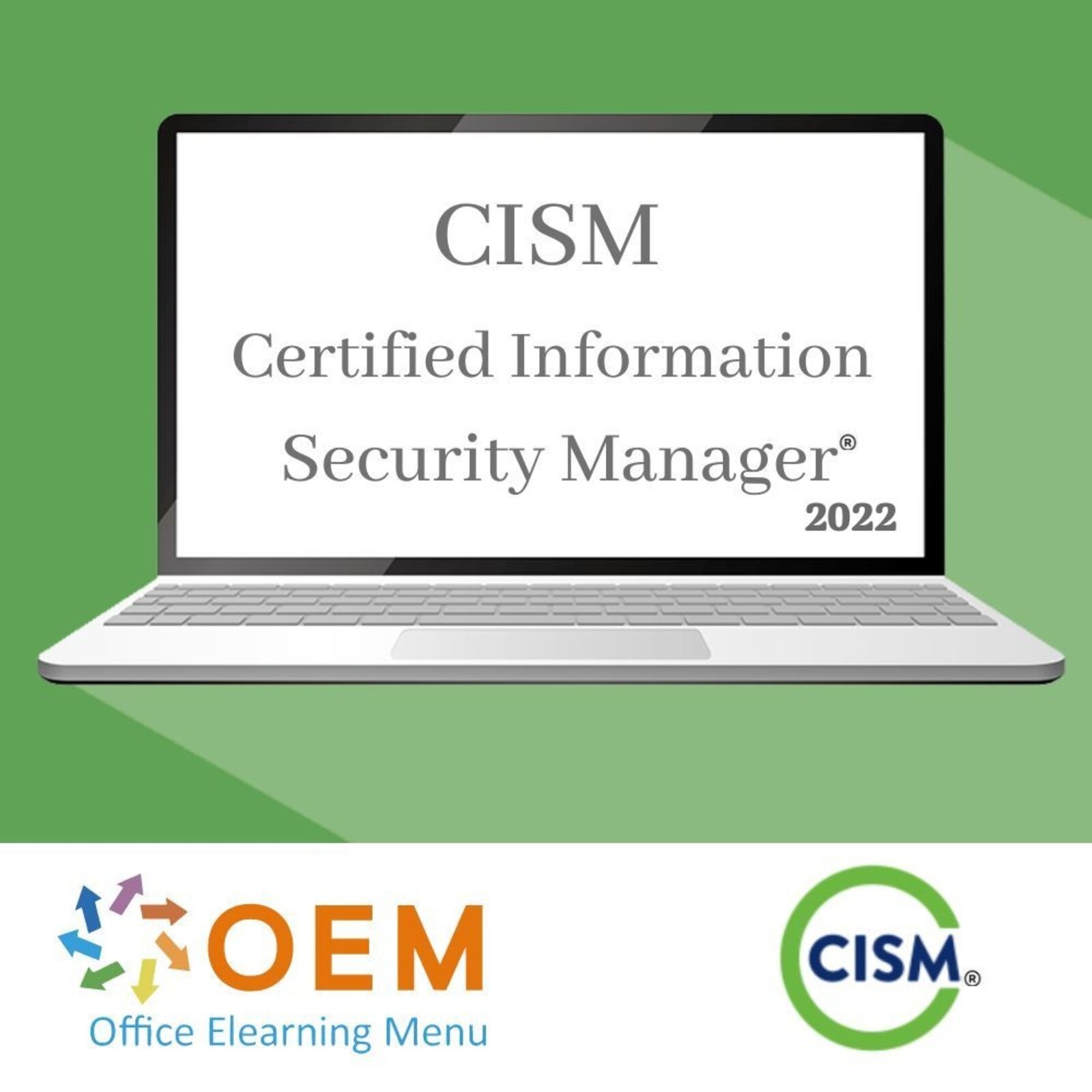
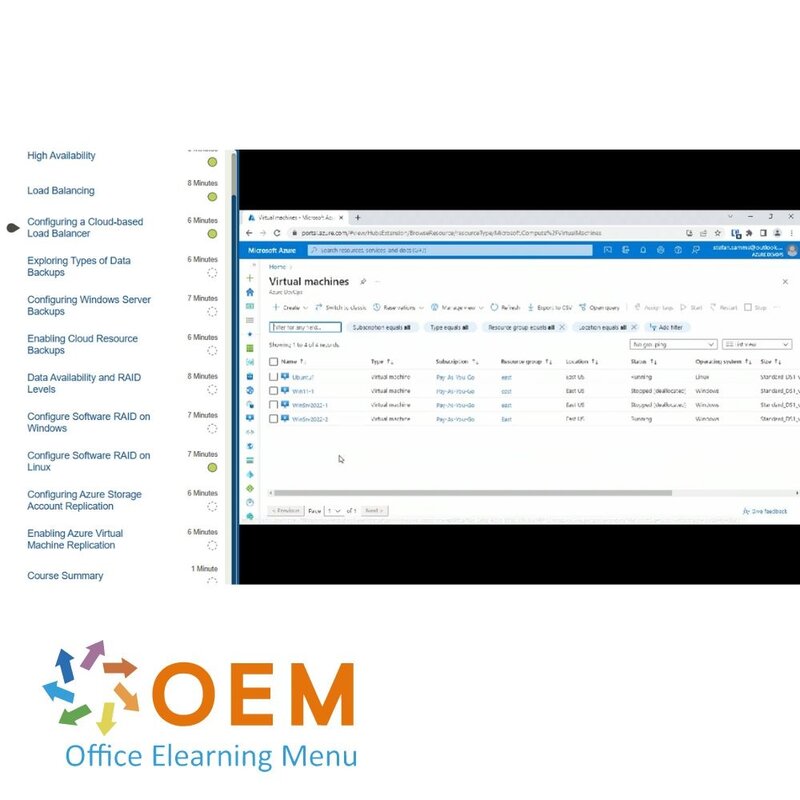
CISM 2022: IT Service & Data Availability
Course: 1 Hour, 17 Minutes
- Course Overview
- High Availability
- Load Balancing
- Configuring a Cloud-based Load Balancer
- Exploring Types of Data Backups
- Configuring Windows Server Backups
- Enabling Cloud Resource Backups
- Data Availability and RAID Levels
- Configure Software RAID on Windows
- Configure Software RAID on Linux
- Configuring Azure Storage Account Replication
- Enabling Azure Virtual Machine Replication
- Course Summary
CISM 2022: Common Network Security Threats
Course: 1 Hour, 15 Minutes
- Course Overview
- Threat Actor Types
- Viewing Common Vulnerabilities and Exposures (CVEs)
- Using the MITRE ATT&CK Knowledge Base
- OWASP Top 10 Web Application Attacks
- Working with Bug Bounties
- Common Wi-Fi Attacks
- SYN Flood Attacks
- Buffer Overflow Attacks
- Advanced Persistent Threat (APT)
- DDoS Attacks
- Using Internet User VPNs and the Tor Web Browser
- Course Summary
CISM 2022: Common Network Security Attacks
Course: 50 Minutes
- Course Overview
- Scanning Networks Using Nmap
- Compromising a Web Browser
- Executing a SQL Injection Attack
- Configuring a Reverse Shell
- Spoofing Network Traffic
- Executing a Distributed Denial-of-service (DDoS) Attack
- Brute Forcing Remote Desktop Protocol (RDP) Connections
- Course Summary
CISM 2022: Cloud Computing & Coding
Course: 50 Minutes
- Course Overview
- Cloud Computing Deployment Models
- Cloud Computing Service Model
- Cloud Computing and Security
- Deploying a Microsoft Azure Blueprint Environment
- The Software Development Life Cycle (SDLC)
- Secure Coding
- SecDevOps
- Course Summary
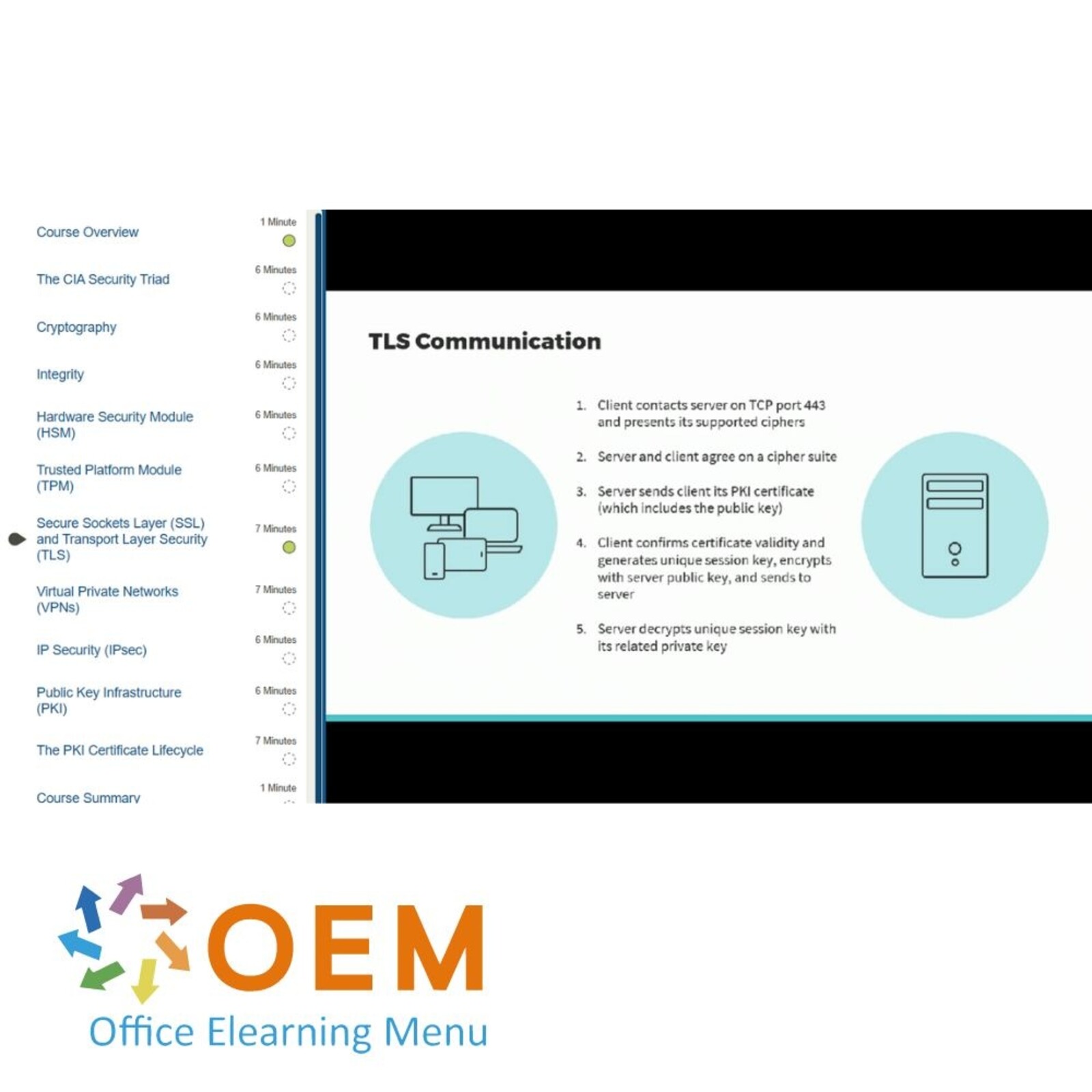
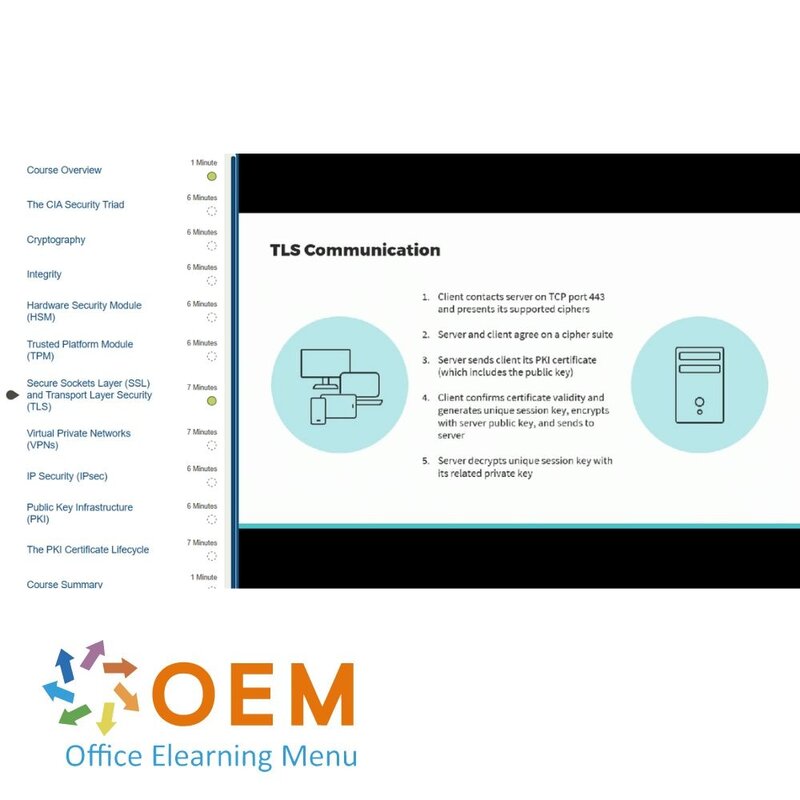
CISM 2022: Data Protection with Cryptography
Course: 1 Hour, 6 Minutes
- Course Overview
- The CIA Security Triad
- Cryptography
- Integrity
- Hardware Security Module (HSM)
- Trusted Platform Module (TPM)
- Secure Sockets Layer (SSL) and Transport Layer Security (TLS)
- Virtual Private Networks (VPNs)
- IP Security (IPsec)
- Public Key Infrastructure (PKI)
- The PKI Certificate Lifecycle
- Course Summary
CISM 2022: Applied Cryptography
Course: 1 Hour, 16 Minutes
- Course Overview
- Generating File System Hashes Using Linux
- Generating File System Hashes Using PowerShell
- Enabling an HTTPS Binding
- Deploying a Private Certificate Authority (CA)
- Managing PKI Certificate Templates
- Acquiring PKI Certificates
- Client PKI Certificates
- Managing Windows Encrypting File System (EFS)
- Managing Microsoft BitLocker
- Managing Linux File System Encryption
- Configuring a Cloud-based User VPN
- Implementing IPsec with Windows
- Course Summary
CISM 2022: Secure Device & OS Management
Course: 1 Hour, 39 Minutes
- Course Overview
- Mobile Device Security
- Mobile Device Remote Wipe
- Centrally Managing Devices
- Securely Wiping Storage Media
- Hardening Windows Stations Using Group Policy
- Disabling SSL on Windows Servers
- Digital Forensics Hardware and Software
- Storage Area Network (SAN) Security
- Implementing a Jump Box Solution
- Configuring Microsoft Azure Managed Identities
- Device and Operating System (OS) Hardening
- Hardening a Wi-Fi Router
- Hardening a Network Printer
- Firmware and Software Patching
- Course Summary
CISM 2022: Social Engineering & Malware
Course: 43 Minutes
- Course Overview
- Social Engineering
- Malware Types
- Reviewing Phishing Attack Email Messages
- Executing a Social Engineering Attack
- Configuring Endpoint Malware Solutions
- Analyzing Infected Files
- Course Summary
CISM 2022: Security Monitoring
Course: 1 Hour, 24 Minutes
- Course Overview
- Reviewing Microsoft Defender For Cloud Recommendations
- Monitoring the Performance of Windows Hosts
- Managing Windows Event Viewer Logs
- Enabling Windows Log Forwarding
- Monitoring the Performance of Linux Hosts
- Managing Linux Logs
- Enabling Linux Log Forwarding
- Reviewing Web Server Access Logs
- Monitoring the Performance of Cloud Services
- Threat Positives and Negatives
- Security Information and Event Management (SIEM)
- Security Orchestration, Automation, and Response (SOAR)
- Using Microsoft Sentinel As a SIEM
- Course Summary
| Language | English |
|---|---|
| Qualifications of the Instructor | Certified |
| Course Format and Length | Teaching videos with subtitles, interactive elements and assignments and tests |
| Lesson duration | 21 Hours |
| Progress monitoring | Yes |
| Access to Material | 365 days |
| Technical Requirements | Computer or mobile device, Stable internet connections Web browsersuch as Chrome, Firefox, Safari or Edge. |
| Support or Assistance | Helpdesk and online knowledge base 24/7 |
| Certification | Certificate of participation in PDF format |
| Price and costs | Course price at no extra cost |
| Cancellation policy and money-back guarantee | We assess this on a case-by-case basis |
| Award Winning E-learning | Yes |
| Tip! | Provide a quiet learning environment, time and motivation, audio equipment such as headphones or speakers for audio, account information such as login details to access the e-learning platform. |
There are no reviews written yet about this product.
OEM Office Elearning Menu Top 2 in ICT-trainingen 2024!
OEM Office Elearning Menu is trots op de tweede plaats in de categorie ICT-trainingen 2024 bij Beste Opleider van Nederland (Springest/Archipel). Dank aan al onze cursisten voor hun vertrouwen!
Reviews
There are no reviews written yet about this product.