Defensive Programming in Java Training
Defensive Programming in Java Training
Defensive Programming in Java Award-winning E-Learning Training Extensive interactive videos with spoken text Certified teachers Practical exercises Certificate.
Read more- Discounts:
-
- Buy 2 for €155,82 each and save 2%
- Buy 3 for €154,23 each and save 3%
- Buy 4 for €152,64 each and save 4%
- Buy 5 for €151,05 each and save 5%
- Buy 10 for €143,10 each and save 10%
- Buy 25 for €135,15 each and save 15%
- Buy 50 for €127,20 each and save 20%
- Availability:
- In stock
- Delivery time:
- Ordered before 5 p.m.! Start today.
- Award Winning E-learning
- Lowest price guarantee
- Personalized service by our expert team
- Pay safely online or by invoice
- Order and start within 24 hours
Defensive Programming in Java E-Learning
Order this amazing, award-winning Defensive Programming in Java E-Learning course online!
✔️ 1 year 24/7 access to comprehensive interactive videos, speeches, practical tasks and progress monitoring.
✔️ Includes a certificate of participation on successful completion.
Why choose this course?
Defensive Programming is an essential skill for any Java developer who wants to build robust, secure and fault-tolerant software. With this course, you will learn how to write code that can withstand adverse and unforeseen circumstances, significantly improving the reliability and security of your software.
What you will learn:
- Defensive programming techniques in Java: Understand the principles of defensive programming and how they can contribute to more secure software.
- Use of assertions and annotations: Learn how to use these tools to better document and secure code.
- Implementing secure classes and methods: Discover best practices to prevent vulnerabilities in your Java applications.
- Prevention of attacks: Understand how to prevent denial of service and injection attacks and process data securely.
- Effective concurrency management: Learn techniques to solve concurrency issues and ensure secure access to shared resources.
- Implement access control: Ensure that only authorised users can access specific parts of your applications.
Who should participate?
This course is perfect for:
- Java developers who want to build secure and reliable applications.
- Software security professionals who want to learn more about defensive programming techniques in Java.
- IT professionals responsible for the security and quality of software applications.
- Team leaders and project managers who want to gain a better understanding of secure development methods.
- Students and beginners who want to learn about the fundamentals of secure programming practices.
Course content
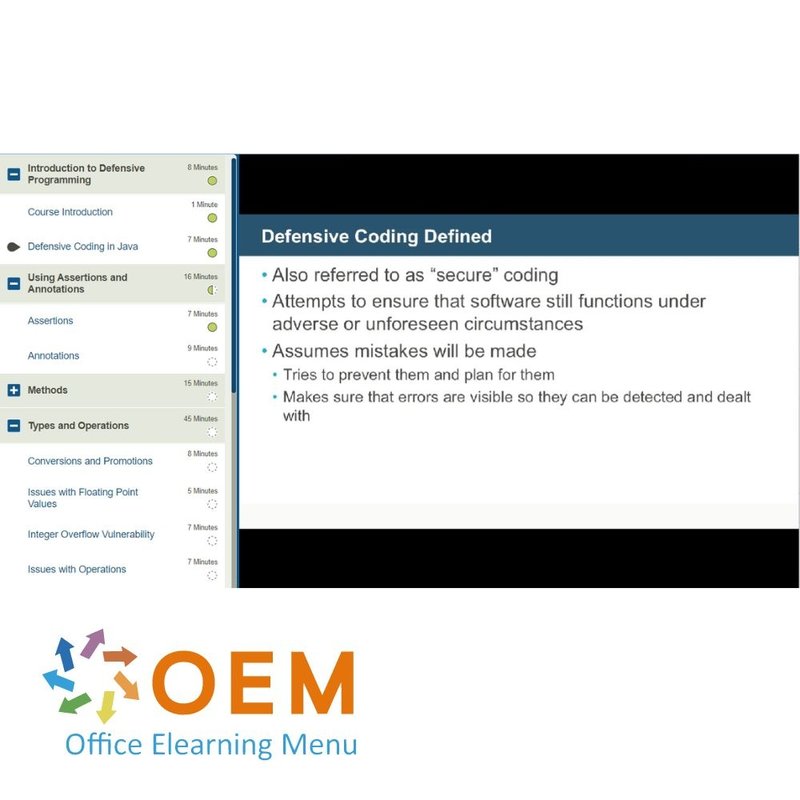
Introduction to Defensive Programming
Course: 8 Minutes
- Course Introduction
- Defensive Coding in Java
Using Assertions and Annotations
Course: 16 Minutes
- Assertions
- Annotations
Methods
Course: 15 Minutes
- Defensible Methods
- Working with Untrusted Parameters
- Checking Return Values
Types and Operations
Course: 45 Minutes
- Conversions and Promotions
- Issues with Floating Point Values
- Integer Overflow Vulnerability
- Issues with Operations
- Strings and Variable-Width Encodings
- Strings and Noncharacter Data
- Strings and Locale-dependent Data
- The Value of Null
Classes and Objects
Course: 34 Minutes
- Working with Classes
- Working with Constructors
- Issues with Mutability
- Serialization and Deserialization
- Object and Reference Equality
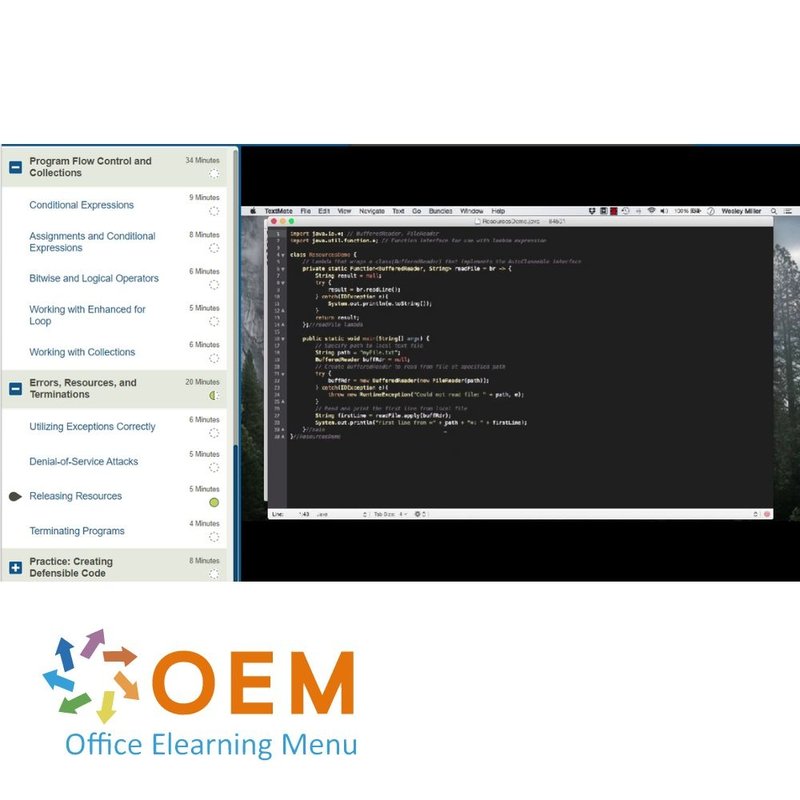
Program Flow Control and Collections
Course: 34 Minutes
- Conditional Expressions
- Assignments and Conditional Expressions
- Bitwise and Logical Operators
- Working with Enhanced for Loop
- Working with Collections
Errors, Resources, and Terminations
Course: 20 Minutes
- Utilizing Exceptions Correctly
- Denial-of-Service Attacks
- Releasing Resources
- Terminating Programs
Practice: Creating Defensible Code
Course: 8 Minutes
- Exercise: Code Defensively in Java
Working with Data
Course: 42 Minutes
- Course Introduction
- Logging Data
- Unsanitized Data and Format Strings
- Working with ZIP Files
- Validating Input
- Using Regular Expressions
Defending against Attacks
Course: 1 Hour, 23 Minutes
- SQL Injection Attacks
- Preventing Code Injections
- Setting Up an LDAP Server
- Preventing LDAP Injection
- Preventing XPath Injections
- Preventing XML Injections
- XML Entity Expansion Attacks
- Defending against Path Traversal Attacks
Concurrency
Course: 31 Minutes
- Race Conditions in Concurrent Programming
- Guaranteeing Safe Publication
- Working with Synchronization Semantics
- Using Thread-Safety-Related Annotations
Practice: Defending Against Attacks
Course: 9 Minutes
- Exercise: Defending Against Attacks
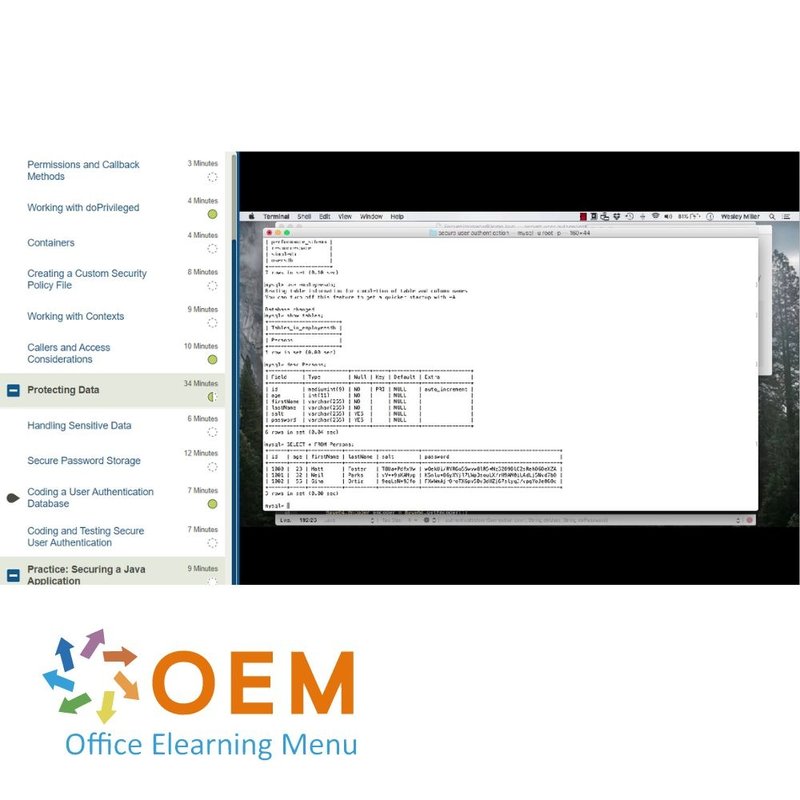
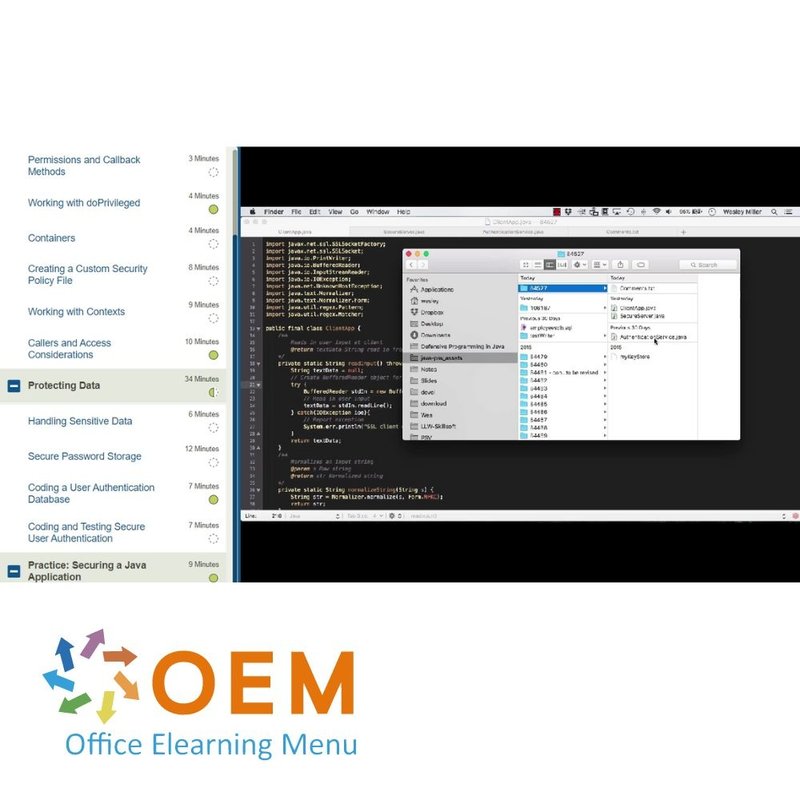
Secure Communications and Access Control
Course: 56 Minutes
- Course Introduction
- Secure Network Communications
- Permissions and Callback Methods
- Working with doPrivileged
- Containers
- Creating a Custom Security Policy File
- Working with Contexts
- Callers and Access Considerations
Protecting Data
Course: 34 Minutes
- Handling Sensitive Data
- Secure Password Storage
- Coding a User Authentication Database
- Coding and Testing Secure User Authentication
Practice: Securing a Java Application
Course: 9 Minutes
- Exercise: Securing Access
Get started with Defensive Programming in Java!
✔️ Learn at your own pace with interactive videos, practical exercises and assignments.
✔️ Test your knowledge with progress monitoring and practical tasks per chapter.
✔️ Improve the security of your code and build robust applications that can withstand various threats.
Order your course now and start developing safe and effective Java applications today!
| Language | English |
|---|---|
| Qualifications of the Instructor | Certified |
| Course Format and Length | Teaching videos with subtitles, interactive elements and assignments and tests |
| Lesson duration | 7:24 Hours |
| Progress monitoring | Yes |
| Access to Material | 365 days |
| Technical Requirements | Computer or mobile device, Stable internet connections Web browsersuch as Chrome, Firefox, Safari or Edge. |
| Support or Assistance | Helpdesk and online knowledge base 24/7 |
| Certification | Certificate of participation in PDF format |
| Price and costs | Course price at no extra cost |
| Cancellation policy and money-back guarantee | We assess this on a case-by-case basis |
| Award Winning E-learning | Yes |
| Tip! | Provide a quiet learning environment, time and motivation, audio equipment such as headphones or speakers for audio, account information such as login details to access the e-learning platform. |
There are no reviews written yet about this product.
OEM Office Elearning Menu Top 2 in ICT-trainingen 2024!
OEM Office Elearning Menu is trots op de tweede plaats in de categorie ICT-trainingen 2024 bij Beste Opleider van Nederland (Springest/Archipel). Dank aan al onze cursisten voor hun vertrouwen!
Reviews
There are no reviews written yet about this product.