OS Exploits Training



OS Exploits Training
OS Exploits E-Learning Training Certified Teachers Exam Quizzes Assessments Test Exam Live Labs Tips Tricks Certificate.
Read more- Discounts:
-
- Buy 2 for €292,04 each and save 2%
- Buy 3 for €289,06 each and save 3%
- Buy 4 for €286,08 each and save 4%
- Buy 5 for €283,10 each and save 5%
- Buy 10 for €268,20 each and save 10%
- Buy 25 for €253,30 each and save 15%
- Buy 50 for €238,40 each and save 20%
- Availability:
- In stock
- Delivery time:
- Ordered before 5 p.m.! Start today.
- Award Winning E-learning
- Lowest price guarantee
- Personalized service by our expert team
- Pay safely online or by invoice
- Order and start within 24 hours
OS Exploits E-Learning
Identify and mitigate vulnerabilities in Windows and Linux environments.
Understanding how operating systems are exploited is a critical step in securing enterprise environments. This course provides deep insight into both Microsoft and Linux OS vulnerabilities, teaching you how to discover, analyze, and resolve security flaws using industry-standard tools and best practices.
What you’ll learn:
- Intelligence gathering and threat discovery
- Common Windows OS and service-based vulnerabilities
- Addressing issues in outdated software environments
- Post-exploitation strategies and security analysis
- Exploiting and analyzing Linux systems and daemons
- Hands-on with Linux-native pentesting tools and architectures
This course is part of an Agile Learning Kit, including e-learning, assessments, mentor guidance, practice labs, and 365-day access.
Why Choose This Training?
- Build expertise in operating system security
- Learn defensive and offensive exploit strategies
- Gain hands-on experience with tools in real-world scenarios
- Dual focus on Windows and Linux systems
- All materials available for 365 days, including mentor and final exams
Who Should Enroll?
This course is ideal for:
- Security professionals and ethical hackers
- System administrators managing Windows/Linux servers
- SOC analysts and cybersecurity teams
- IT professionals aiming to specialize in OS security
This Learning Kit, with more than 14 hours of online content, is divided into the following tracks:
Course content
E-learning courses (14 hours +)
Windows Exploits and Forensics: Intelligence Gathering
Course: 1 Hour, 28 Minutes
- Course Overview
- The Open-source Intelligence (OSINT) Methodology
- Conducting an OSINT Investigation
- Social Engineering Target Identification
- Network Scanning for Open Ports
- Conducting an Nmap Scan
- Common Windows Services and Their Ports
- System Scanning and Enumeration Tools
- Conducting a Windows System Scan
- Standard Kali Tools
- Using Metasploitable: Common Commands and Issues
- Windows Exploit Discovery
- Course Summary
Windows Exploits and Forensics : Windows Environments
Course: 1 Hour, 32 Minutes
- Course Overview
- The Security Features and Controls on Windows Hosts
- Windows Server Operating System Types
- Intrusion Detection and Prevention in Windows
- The MITRE ATT&CK Framework and Windows Intrusions
- The Logging Features in Windows
- Viewing Event logging
- The Different Windows Account Types
- Using Windows Commands
- How Windows Permissions Work
- NT (New Technology) LAN Manager (NTLM) in Windows
- Cracking an NTLM Hash
- Using the Windows Registry
- Artifacts Found in Windows OS
- How Active Directory and Kerberos Work
- Course Summary
Windows Exploits and Forensics: SMB & PsExec
Course: 1 Hour, 6 Minutes
- Course Overview
- SMB Permissions and Defaults
- SMB Enumeration
- Enumerating SMB Shares
- Identifying Vulnerabilities in SMB
- SMB Attack Methods
- Conducting an SMB Brute Force Attack
- Conducting an SMB Denial of Service
- Exploiting a System Using SMB Reverse Shell
- How the PsExec Utility Works
- Executing Remote Commands with PsTools
- Executing a Pass the Hash Attack with Mimikatz
- A Background to the EternalBlue Exploit
- Using the EternalBlue Vulnerability to Attack
- Course Summary
Windows Exploits and Forensics: FTP, RDP, & Other Services
Course: 1 Hour, 13 Minutes
- Course Overview
- Windows Service Exploitation
- Enumerating Data from FTP
- FTP Attack Methods
- Conducting a Brute Force Attack on an FTP Server
- IIS with Windows and FTP Clients
- FTP/IIS Reverse Shell
- RDP in a Windows Environment
- RDP Attack Methods
- Enumerating Using RDP
- Exploiting an RDP system Using BlueKeep
- Working with WMI
- Exploiting WMI on a Windows-based System
- Course Summary
Windows Exploits and Forensics: Legacy Systems & Third Party Applications
Course: 58 Minutes
- Course Overview
- Common Attacks on Windows Hosts
- Common Attacks on Windows Servers
- Scanning for Potential Vulnerabilities
- Enumerating Data from Services
- Running an Exploit to Gain Credentials
- Running an Exploit to Gain a Reverse Shell
- Common Third-party Applications in Windows
- Finding Vulnerabilities for Third-party Applications
- Exploiting Third-party Applications in Windows
- Avoiding Honeypots
- Course Summary
Windows Exploits and Forensics: Post Exploitation
Course: 1 Hour, 24 Minutes
- Course Overview
- Privilege Escalation Methods
- Conducting a Basic Privilege Escalation
- Using the DLL Injection
- Pivot between Hosts
- Stealing User Credentials
- Using PowerView to Enumerate Information
- Using BloodHound to Gain Admin Privileges
- Cleanup Methods to Hide Your Tracks
- Cleaning up Post Attack
- APT and Configuration Methods
- Configuring APT after Exploitation
- Using the Nuclear Option to Clean up Post Attack
- Course Summary
Linux Exploits & Mitigation: Staging for Exploit Analysis
Course: 1 Hour, 5 Minutes
- Course Overview
- Leveraging Virtual Environments
- Setting up QEMU
- Launching Linux in QEMU
- Mounting Filesystems
- Compiling Linux Kernels
- Networking under QEMU
- Architectural Considerations
- Emulating Architectures in QEMU
- Saving Machine States
- Monitoring System Info
- Staging Vulnerabilities
- Protecting Staging Environments
- Course Summary
Linux Exploits & Mitigation: Program Essentials
Course: 1 Hour, 21 Minutes
- Course Overview
- Programming in Memory
- Running GDB
- Disassembling a Program
- Dumping Objects
- Protection Rings
- Kernel and Userland Separation
- The GNU C Library
- Using Syscalls with C
- Using Syscalls with Assembly
- Linux System Call Table
- Querying Implemented System Calls
- Executing Programs
- Segmenting Programs
- Course Summary
Linux Exploits & Mitigation: String Vulnerability Analysis
Course: 1 Hour, 10 Minutes
- Course Overview
- Exploiting Strings
- Formatting String Weaknesses
- Overflowing the String Buffer
- Compiling String Weaknesses
- Copying String Weaknesses
- Catching Input Vulnerabilities
- Generating String Weaknesses
- Checking Strings Safely
- Looping Over Strings Safely
- Executing Unsafe Strings
- Injecting Code in Strings
- Returning Strings Safely
- Course Summary
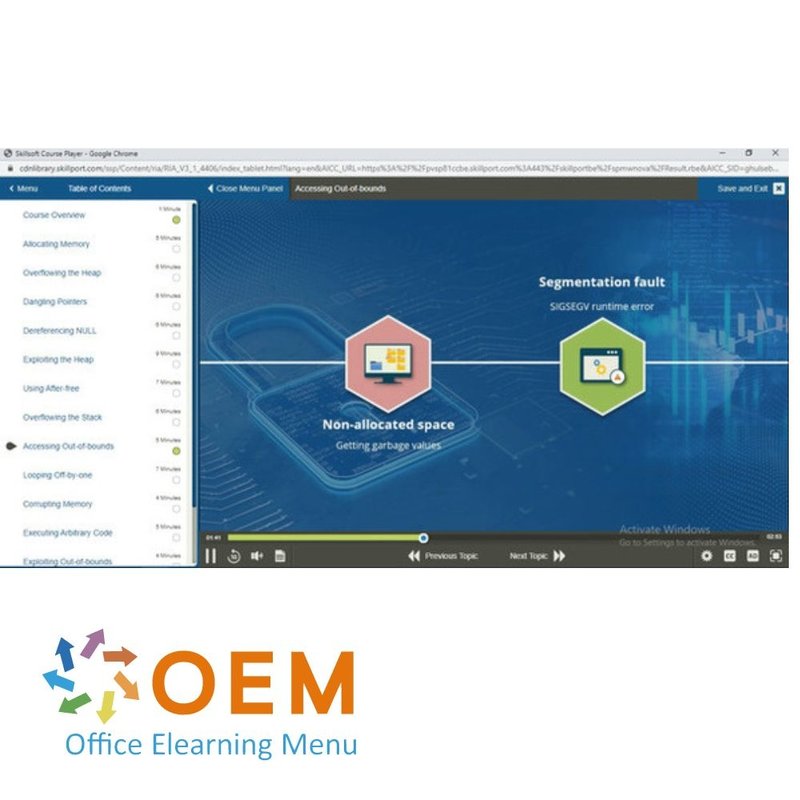
Linux Exploits & Mitigation: Memory and Pointer Vulnerabilities
Course: 1 Hour, 11 Minutes
- Course Overview
- Allocating Memory
- Overflowing the Heap
- Dangling Pointers
- Dereferencing NULL
- Exploiting the Heap
- Using After-free
- Overflowing the Stack
- Accessing Out-of-bounds
- Looping Off-by-one
- Corrupting Memory
- Executing Arbitrary Code
- Exploiting Out-of-bounds
- Course Summary
Linux Exploits & Mitigation: Penetration Tools
Course: 1 Hour
- Course Overview
- Exploring Metasploit Commands
- Running a Vulnerable Environment
- Exploiting a Vulnerable Web Service
- Scanning SMTP
- Exploiting Vulnerable File Sharing
- Uploading Injections
- Searching for Exploits
- Detecting Exploits
- Scanning with RouterSploit
- Inspecting Opcodes
- Converting Shellcode
- SQL Injection
- Course Summary
Linux Exploits & Mitigation: Linux Exploit Architecture
Course: 57 Minutes
- Course Overview
- Avoiding Kernel Race Conditions
- Executing Shellcode
- Out-of-order Execution
- Integer Vulnerabilities and Prevention
- Compiler Warnings for Security and Stability
- Stack Smashing Mitigations
- Use-after-free Consequences
- Spectre and Meltdown Vulnerabilities and Mitigation
- Write XOR Execute (W^X)
- Considerations and Mitigations to Vulnerabilities and Exploits
- Privilege Escalation Targets
- Processes and Tasks Exploits
- Course Summary
Assessment: OS Exploits
Will test your knowledge and application of the topics presented throughout the OS Exploits courses.
Practice Lab: OS Exploits (estimated duration: 7 hours)
Perform OS exploits such as system event auditing, testing for RDP vulnerabilities, constructing a MSFvenom injection payload, and running a virtual environment. Then, debug and disassemble a program, catch common vulnerabilities, and recognize the dangers with pointers.
| Language | English |
|---|---|
| Qualifications of the Instructor | Certified |
| Course Format and Length | Teaching videos with subtitles, interactive elements and assignments and tests |
| Lesson duration | 14 Hours |
| Assesments | The assessment tests your knowledge and application skills of the topics in the learning pathway. It is available 365 days after activation. |
| Online Virtuele labs | Receive 12 months of access to virtual labs corresponding to traditional course configuration. Active for 365 days after activation, availability varies by Training |
| Online mentor | You will have 24/7 access to an online mentor for all your specific technical questions on the study topic. The online mentor is available 365 days after activation, depending on the chosen Learning Kit. |
| Progress monitoring | Yes |
| Access to Material | 365 days |
| Technical Requirements | Computer or mobile device, Stable internet connections Web browsersuch as Chrome, Firefox, Safari or Edge. |
| Support or Assistance | Helpdesk and online knowledge base 24/7 |
| Certification | Certificate of participation in PDF format |
| Price and costs | Course price at no extra cost |
| Cancellation policy and money-back guarantee | We assess this on a case-by-case basis |
| Award Winning E-learning | Yes |
| Tip! | Provide a quiet learning environment, time and motivation, audio equipment such as headphones or speakers for audio, account information such as login details to access the e-learning platform. |
There are no reviews written yet about this product.
OEM Office Elearning Menu Top 2 in ICT-trainingen 2024!
OEM Office Elearning Menu is trots op de tweede plaats in de categorie ICT-trainingen 2024 bij Beste Opleider van Nederland (Springest/Archipel). Dank aan al onze cursisten voor hun vertrouwen!
Reviews
There are no reviews written yet about this product.