Prompt Engineering for Ethical Hacking Training

Prompt Engineering for Ethical Hacking Training
Prompt Engineering for Ethical Hacking E-Learning Training Certified teachers Quizzes Assessments Tips tricks and Certificate.
Read more- Discounts:
-
- Buy 2 for €194,04 each and save 2%
- Buy 3 for €192,06 each and save 3%
- Buy 4 for €190,08 each and save 4%
- Buy 5 for €188,10 each and save 5%
- Buy 10 for €178,20 each and save 10%
- Buy 25 for €168,30 each and save 15%
- Buy 50 for €158,40 each and save 20%
- Availability:
- In stock
- Delivery time:
- Ordered before 5 p.m.! Start today.
- Award Winning E-learning
- Lowest price guarantee
- Personalized service by our expert team
- Pay safely online or by invoice
- Order and start within 24 hours
Prompt Engineering for Ethical Hacking E-Learning
Fuse the power of Ethical Hacking with Prompt Engineering and Generative AI.
This forward-thinking course takes the proven foundation of Ethical Hacking and reinvents it through the lens of Prompt Engineering and Generative AI. While you'll still cover essential cybersecurity principles and tools, you’ll also explore how AI is revolutionizing the way ethical hackers gather intel, analyze systems, and simulate attacks and defenses.
You'll learn how to craft effective prompts to automate tasks, interpret vulnerabilities, and even simulate social engineering — all using AI platforms like ChatGPT and beyond.
Why Choose This Training?
-
Master core Ethical Hacking concepts enhanced with AI
-
Learn to use Prompt Engineering with ChatGPT, Bard, etc.
-
Discover how AI is transforming the cybersecurity landscape
-
Apply AI to red and blue teaming operations
-
365-day access to labs, mentor support, final exams, and e-learning
Who Should Enroll?
This training is ideal for:
-
Ethical hackers and penetration testers seeking to leverage AI
-
Cybersecurity professionals wanting a competitive edge
-
Students and early-career analysts with basic security knowledge
-
IT managers exploring AI integrations into their cyber strategy
This Learning Kit with more than 12 hours of learning is divided into three tracks:
Course content
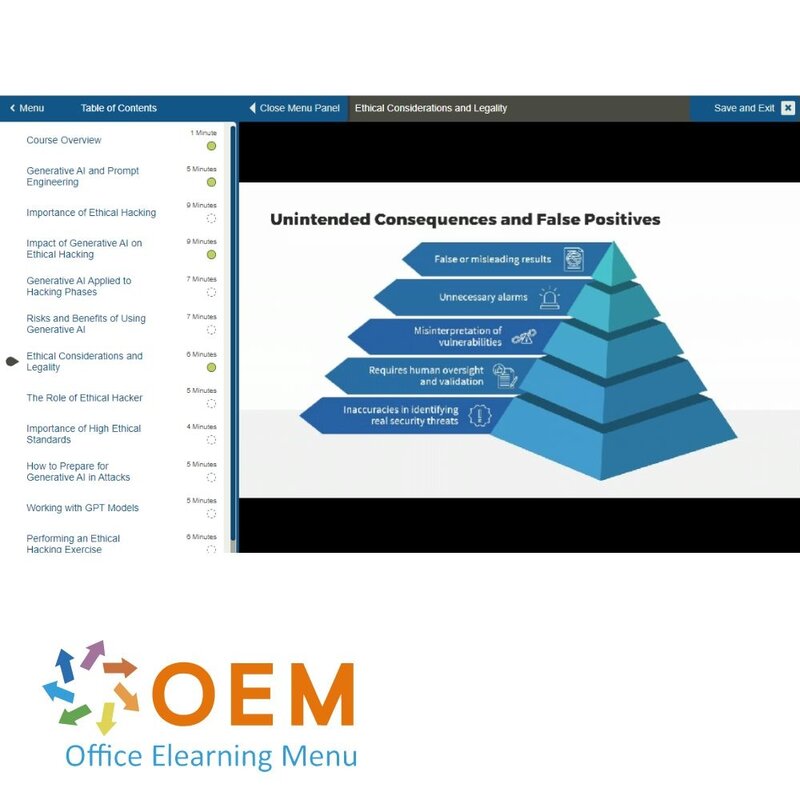
Prompt Engineering: Ethical Hacking & Generative AI Fusion
In our increasingly digital world, the convergence of ethical hacking and generative AI technologies has become a crucial frontier in cybersecurity. As technology advances, so do the methods employed by hackers, making it essential for ethical hackers, or white hat hackers, to stay one step ahead. This course introduces you to the exciting world of ethical hacking and generative AI technologies.
Course: 1 Hour, 20 Minutes
- Course Overview
- Generative AI and Prompt Engineering
- Importance of Ethical Hacking
- Impact of Generative AI on Ethical Hacking
- Generative AI Applied to Hacking Phases
- Risks and Benefits of Using Generative AI
- Ethical Considerations and Legality
- The Role of Ethical Hacker
- Importance of High Ethical Standards
- How to Prepare for Generative AI in Attacks
- Working with GPT Models
- Performing an Ethical Hacking Exercise
- Identify Potential Attacks
- Course Summary
Prompt Engineering: Generative AI for Reconnaissance
In today's rapidly evolving digital landscape, the convergence of ethical hacking and generative AI has emerged as a powerful force in countering cybersecurity threats. As malicious hackers adapt and exploit advanced technologies, the need for innovative defenses becomes paramount. This course explores the cutting-edge domain of generative artificial intelligence (AI) and reconnaissance techniques.
Course: 52 Minutes
- Course Overview
- Reconnaissance Techniques
- Prompt Engineering for Information Gathering
- Methods and Tools for Reconnaissance
- Benefits of Reconnaissance to Ethical Hacking
- Performing Passive Reconnaissance
- Performing Active Reconnaissance
- Challenges and Solutions in Reconnaissance
- Protecting Against Reconnaissance
- Prompt Engineering for Reconnaissance
- Apply Information From Reconnaissance
- Course Summary
Prompt Engineering: Generative AI for Scanning & Enumeration
As technology continues to advance, hackers are constantly adapting their methods, making it imperative for ethical hackers to stay one step ahead. This course explores the convergence of ethical hacking and generative AI, specifically focusing on the scanning and enumeration phase of the ethical hacking process.
Course: 1 Hour, 6 Minutes
- Course Overview
- Network Scanning and Enumeration
- Combine Scanning Tools and Generative AI
- Prompt Engineering to Optimize Scanning
- Performing Scans Leveraging Generative AI
- Information Quality and AI-assisted Scanning
- AI-informed Measures and Risk of Exploitation
- Leveraging Generative AI for Enumeration
- Significance of Generative AI
- How Scanning Techniques Are Improved
- Case Studies Involving Scanning and Enumeration
- Course Summary
Prompt Engineering: Generative AI for System Hacking
Ethical hackers are key to maintaining a robust cybersecurity posture, and must commit to continuous improvement to stay ahead of malicious actors. This course provides an immersive journey into the techniques and methodologies employed by ethical hackers to protect and secure systems while focusing on generative artificial intelligence (AI) as a transformative resource in the hacking toolchain.
Course: 1 Hour, 9 Minutes
- Course Overview
- System Hacking and Generative AI
- Enhancing Attacks with Generative AI
- Calculating CVSS Score for System Vulnerabilities
- Best Practices to Protect Against System Hacking
- How Generative AI Protects Against System Hacking
- Using Generative AI to Drive Penetration Tests
- Real-world System Hacking Scenarios
- Impact of Generative AI on System Hacking
- Generating Vulnerability Reports and Recommendations
- Transformative Potential of Generative AI
- Course Summary
Prompt Engineering: Generative AI for Malware & Social Engineering
This course journeys deep into the techniques and methodologies employed by ethical hackers to uncover malware and educate users in the ongoing battle against social engineering and how generative artificial intelligence (AI) can assist them in this pursuit.
Course: 1 Hour, 5 Minutes
- Course Overview
- Types of Malware
- Social Engineering
- Generating Phishing Emails
- Detecting Social Engineering Attacks
- Potential Damage From Attack
- Countermeasures Against Attack
- User Training on Social Engineering Attacks
- Conducting a Social Engineering Attack
- The Evolution of Malware and Social Engineering
- Real-world Case Studies
- Course Summary
Prompt Engineering: GenAI’s Impact on Network & Perimeter Ethical Hacking
Begin by exploring the fundamentals of network and perimeter hacking, typical network attack techniques, and how these attacks can be enhanced using generative AI.
Course: 1 Hour, 22 Minutes
- Course Overview
- Fundamentals of Network and Perimeter Hacking
- Types of Attacks on Networks
- AI-aided Countermeasures Against Attack
- Enhanced Attacks Employing Generative AI
- Impact on Attack and Defensive Strategies
- Network Security Hardware and Software
- Enhancing Wired Network Vulnerability Discovery
- The Importance of Network Perimeter Security
- Network and Perimeter Hacking Case Studies
- Monitoring and Analyzing Wireless Network Activity
- Performing Generative AI-driven Attacks
- Course Summary
Prompt Engineering: Web Application & Database Hacking in the Age of GenAI
This course is a comprehensive journey into the tools and techniques available to ethical hackers to discover vulnerabilities and weaknesses in web applications and databases. Particular attention will be paid to how generative artificial intelligence (AI) can help in the discovery and mitigation of attacks on these technologies, including those enhanced by integrating AI in the attack.
Course: 1 Hour, 47 Minutes
- Course Overview
- Common Web Application Vulnerabilities
- Exploiting and Mitigating Web Vulnerabilities
- Common Database Vulnerabilities
- Exploiting and Mitigating Database Vulnerabilities
- Common Database Hacking Techniques
- Enhanced Web and Database Security
- Performing AI-assisted SQL Injection Attacks
- Web and Database Security Solutions
- Strategies to Secure Web Applications and Databases
- Detecting Web Application Vulnerabilities
- Implications of AI-enhanced Web and Database Hacking
- The Importance of Regular Updates and Patches
- Web and Database Hacking Case Studies
- Course Summary
Prompt Engineering: Cloud Computing & IoT Hacking in the Era of GenAI
This course dives deep into the interplay between Cloud computing, IoT, and generative artificial intelligence (AI), shedding light on their collective vulnerabilities and potential and demonstrating how generative AI can be both a formidable adversary and a powerful ally.
Course: 1 Hour, 43 Minutes
- Course Overview
- Common Cloud Service Vulnerabilities
- Cloud Service Exploitation and Protection
- Common IoT Device Vulnerabilities
- IoT Device Exploitation and Protection
- Cloud and IoT Device Hacking Methods
- Mitigation of Cloud and IoT-based Threats
- AI-assisted Hacking of Cloud Services
- Security Best Practices for Cloud and IoT Devices
- Evaluating Generative AI Security Measures
- Identifying and Mitigating IoT Vulnerabilities
- Trends and Advancements in Cloud and IoT Security
- Cloud and IoT Hacking Case Studies
- Course Summary
Prompt Engineering: Mobile Platform Security in the GenAI Era
With AI-driven functionalities at the forefront of mobile technology innovation, understanding the security implications and nuances is paramount. In this course, explore common mobile platform vulnerabilities and utilize generative AI to bolster mobile security measures.
Course: 1 Hour, 13 Minutes
- Course Overview
- Common Vulnerabilities in Mobile Platforms
- Mobile Platform Hacking Techniques
- Mitigate and Exploit Mobile Vulnerabilities
- Enhancing Mobile Platform Security Measures
- Executing an AI-assisted Mobile Platform Hack
- Evaluate Mobile Platform Security Measures
- Educate Users about Mobile Platform Security
- Identifying and Patching Mobile App Vulnerabilities
- The Impact of AI-enhanced Mobile Platform Hacking
- The Importance of Regular Updates and Patches
- Mobile Platform Hacking Case Studies
- Course Summary
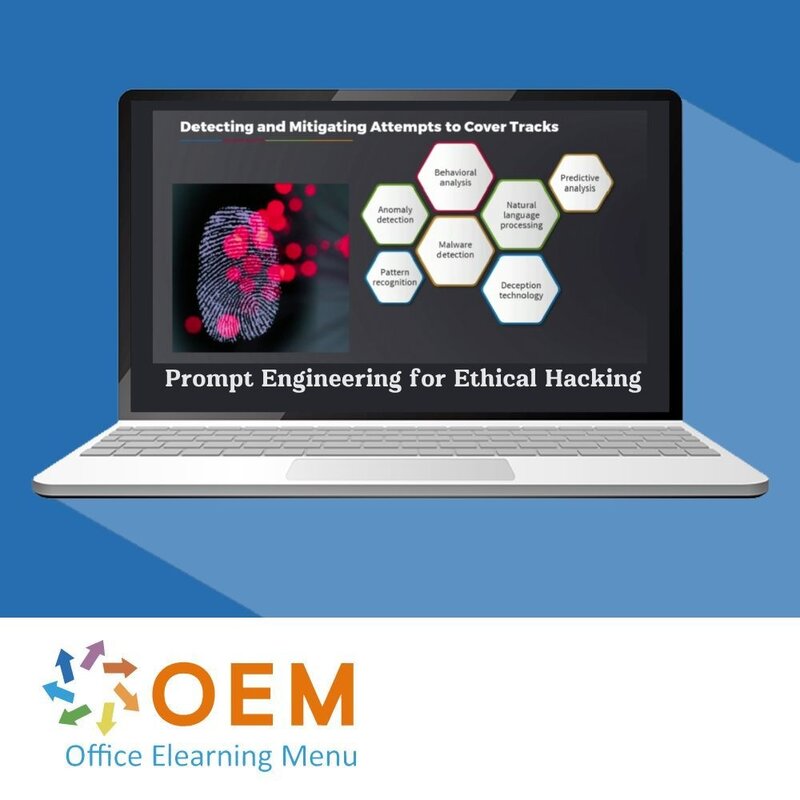
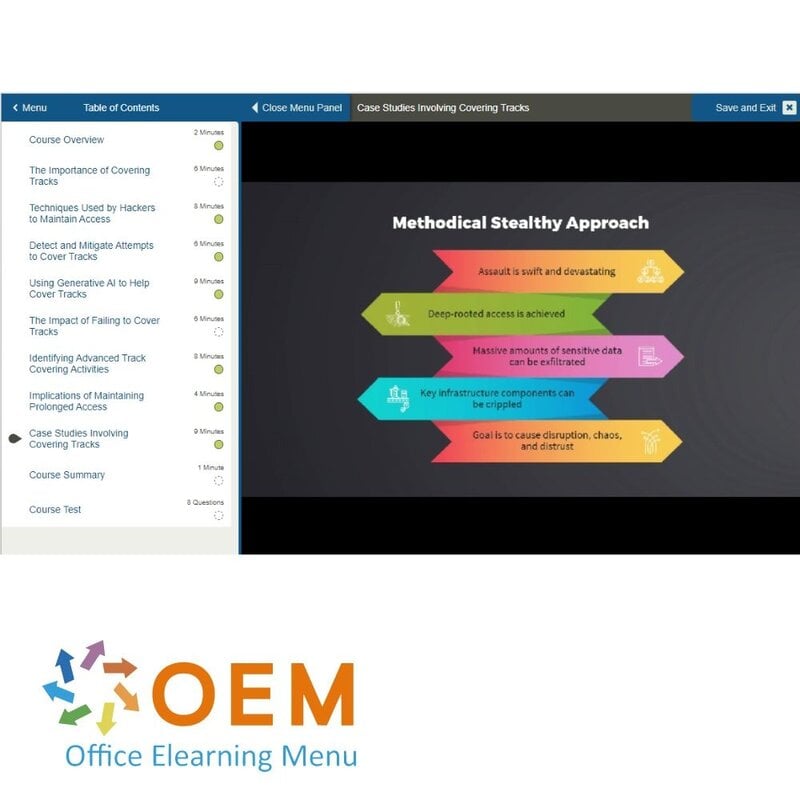
Prompt Engineering: Covering Tracks with GenAI
This course examines the fusion of traditional stealth techniques in hacking with the cutting-edge capabilities of generative AI, looking at how generative AI can be harnessed to leave no digital footprint, ensuring prolonged access to compromised systems.
Course: 58 Minutes
- Course Overview
- The Importance of Covering Tracks
- Techniques Used by Hackers to Maintain Access
- Detect and Mitigate Attempts to Cover Tracks
- Using Generative AI to Help Cover Tracks
- The Impact of Failing to Cover Tracks
- Identifying Advanced Track Covering Activities
- Implications of Maintaining Prolonged Access
- Case Studies Involving Covering Tracks
- Course Summary
Assessment:
Final Exam: Prompt Engineering for Ethical Hacking
| Language | English |
|---|---|
| Qualifications of the Instructor | Certified |
| Course Format and Length | Teaching videos with subtitles, interactive elements and assignments and tests |
| Lesson duration | 12:35 Hours |
| Assesments | The assessment tests your knowledge and application skills of the topics in the learning pathway. It is available 365 days after activation. |
| Online Virtuele labs | Receive 12 months of access to virtual labs corresponding to traditional course configuration. Active for 365 days after activation, availability varies by Training |
| Online mentor | You will have 24/7 access to an online mentor for all your specific technical questions on the study topic. The online mentor is available 365 days after activation, depending on the chosen Learning Kit. |
| Progress monitoring | Yes |
| Access to Material | 365 days |
| Technical Requirements | Computer or mobile device, Stable internet connections Web browsersuch as Chrome, Firefox, Safari or Edge. |
| Support or Assistance | Helpdesk and online knowledge base 24/7 |
| Certification | Certificate of participation in PDF format |
| Price and costs | Course price at no extra cost |
| Cancellation policy and money-back guarantee | We assess this on a case-by-case basis |
| Award Winning E-learning | Yes |
| Tip! | Provide a quiet learning environment, time and motivation, audio equipment such as headphones or speakers for audio, account information such as login details to access the e-learning platform. |
There are no reviews written yet about this product.
OEM Office Elearning Menu Top 2 in ICT-trainingen 2024!
OEM Office Elearning Menu is trots op de tweede plaats in de categorie ICT-trainingen 2024 bij Beste Opleider van Nederland (Springest/Archipel). Dank aan al onze cursisten voor hun vertrouwen!
Reviews
There are no reviews written yet about this product.