Security Threat Intelligence Training



Security Threat Intelligence Training
Security Threat Intelligence E-Learning Training Gecertificeerde docenten Quizzen Assessments test examen Live Labs Tips trucs Certificaat.
Lees meer- Beschikbaarheid:
- Op voorraad
- Levertijd:
- Voor 17:00 uur besteld! Start vandaag. Gratis Verzending.
- Award Winning E-learning
- De laagste prijs garantie
- Persoonlijke service van ons deskundige team
- Betaal veilig online of op factuur
- Bestel en start binnen 24 uur
Security Threat Intelligence E-Learning Training
Ontwikkel cyberinlichtingenvaardigheden om digitale dreigingen voor te blijven.
In een wereld vol geavanceerde cyberdreigingen is reactief handelen niet meer voldoende. Met deze training leer je hoe je proactief bedreigingen kunt opsporen, analyseren en aanpakken met behulp van threat intelligence. Ontdek hoe je organisaties beschermt tegen interne én externe aanvallen, en bouw expertise op in netwerk- en forensisch onderzoek, malwareverwijdering en defensieve cyberoperaties.
Wat je leert:
-
Inlichtingen verzamelen over dreigingen en aanvalspatronen
-
Analyseren van netwerken, hosts en verdachte activiteiten
-
Malwaredetectie en -verwijdering
-
Toepassen van forensische technieken en CyberOps-principes
-
Best practices in threat attribution en security programming
Deze training maakt deel uit van een Agile Learning Kit, met e-learning, labs, mentorondersteuning en toegang tot alle content gedurende 365 dagen.
Waarom kiezen voor deze opleiding?
-
Leer hoe je proactief cyberdreigingen identificeert en neutraliseert
-
Verdiep je in netwerkonderzoek, forensische analyse en threat attribution
-
Ontwikkel een inlichtingenstrategie voor je organisatie
-
Inclusief labs, assessments, mentor en 365 dagen toegang
-
Ideaal voor wie verder wil gaan dan basisbeveiliging
Wie zou moeten deelnemen?
Deze training is ideaal voor:
-
Cybersecurityprofessionals die willen doorgroeien in threat intelligence
-
Netwerk- en systeembeheerders die verantwoordelijk zijn voor detectie en monitoring
-
SOC-analisten en incident responders
-
Beveiligingsteams binnen zowel overheid als private organisaties
Deze Learning Kit met meer dan 23 leeruren is verdeeld in drie sporen:
Demo Security Threat Intelligence Training
Cursusinhoud
E-learning courses (22 hours +)
CyberOps: Introduction to CyberOps
Course: 54 Minutes
- Course Overview
- Introduction to Defensive Cyber Operations
- Introduction to Offensive Cyber Operations
- Using Nessus to Perform a Vulnerability Scan
- Using Metasploit to Attack Systems
- Comparing OCO with DCO Operations
- Introducing the Cyber Operations Cycle
- Phases of the Cyber Operations Cycle
- Offensive Team Roles
- Defensive Team Roles
- Supporting Team Roles
- Course Summary
Security Programming: Command Line Essentials
Course: 58 Minutes
- Course Overview
- Command Line Properties
- Bash Properties
- PowerShell Environment
- Text Editing Basics
- Text Processing
- Bash History
- Process Management
- Scheduled Jobs
- File Monitoring
- File Comparison
- Redirecting Input and Output
- Package Management
- Course Summary
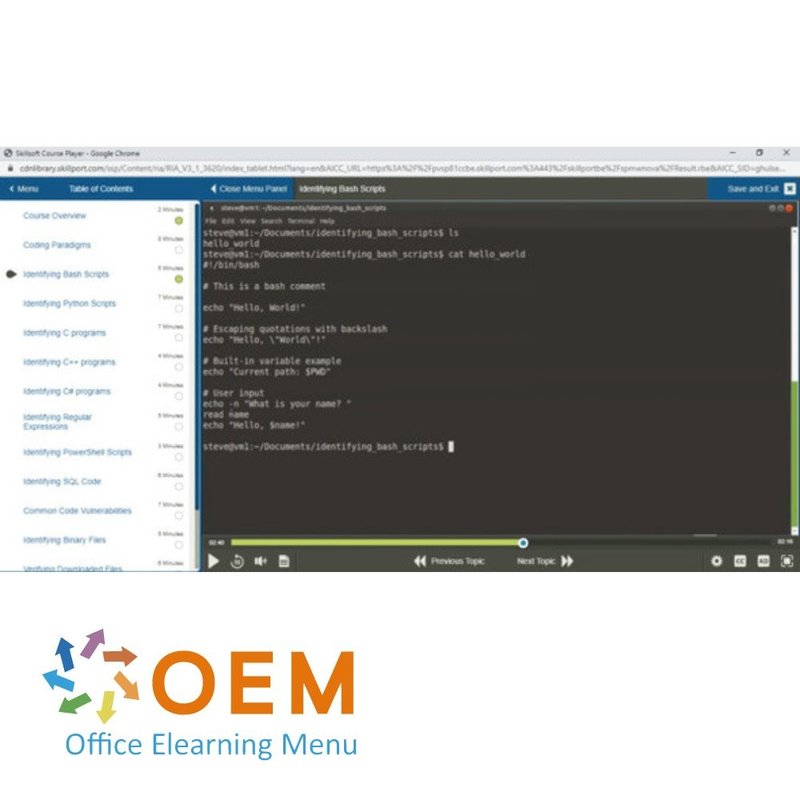
Security Programming: Code Identification
Course: 1 Hour, 9 Minutes
- Course Overview
- Coding Paradigms
- Identifying Bash Scripts
- Identifying Python Scripts
- Identifying C programs
- Identifying C++ programs
- Identifying C# programs
- Identifying Regular Expressions
- Identifying PowerShell Scripts
- Identifying SQL Code
- Common Code Vulnerabilities
- Identifying Binary Files
- Verifying Downloaded Files
- Course Summary
Security Programming: Scripting Essentials
Course: 1 Hour, 1 Minute
- Course Overview
- Introduction to Scripting
- Bash Variables
- Bash Conditionals
- Bash Loops
- Bash Functions
- Python Variables
- Python Conditionals
- Python Loops
- Python Functions
- Python Imports
- Python File Operations
- Python Web Requests
- Course Summary
Security Programming: System Essentials
Course: 57 Minutes
- Course Overview
- Remote Shell Access
- User Accounts
- IP Routing
- Network Interfaces
- Domain Names
- Log Files
- Process Reporting
- Disk Use
- User Activity
- System Activity
- Time and Date Services
- /etc Configurations
- Course Summary
Malware Removal: Identifying Malware Types & Classification Approaches
Course: 26 Minutes
- Course Overview
- Introduction to Traditional Malware Types
- Understanding Worm and Trojan Viruses
- Identifying Rootkits, Botnets, and Ransomware
- Understanding Malware Symptoms
- Tools to Fight Against Malware
- Classifying the Severity of Malware
- Course Summary
Malware Removal: Analyzing an Infected System
Course: 1 Hour, 45 Minutes
- Course Overview
- Why Analyze Malware
- Introduction to Static Analysis
- Introduction to Dynamic Analysis
- Malware Characteristics
- Static Malware Analysis
- Dynamic Malware Analysis
- Malware Impacts
- Ports and Processes Used By Malware
- Process Monitor
- Wireshark
- Malicious Code and Program Flow
- Course Summary
Malware Removal: Remediate an Infected System
Course: 50 Minutes
- Course Overview
- Symptoms of an Infected System
- Best Practices for Malware Removal
- Remediation Approaches for Malware
- Windows Malicious Software Removal Tool
- Using Restore Points
- Using Windows Repair Tools with Restore Points
- Restoring a System Backup
- Comparing Virus Removal to Complete Re-install
- Viruses Affecting your Boot Environment
- Using Windows Repair Tools to Solve Boot Issues
- Course Summary
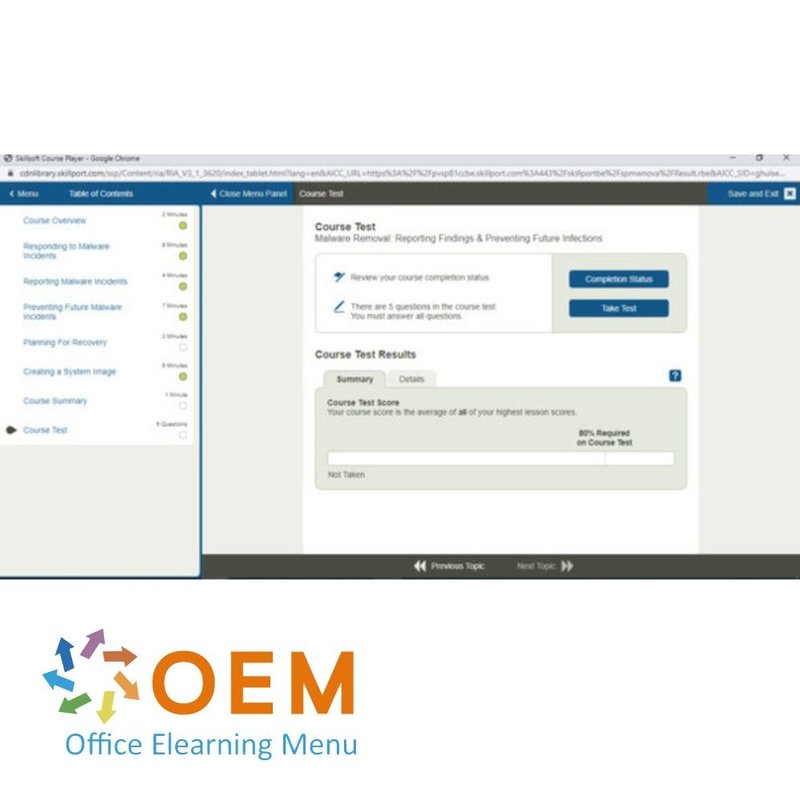
Malware Removal: Reporting Findings & Preventing Future Infections
Course: 31 Minutes
- Course Overview
- Responding to Malware Incidents
- Reporting Malware Incidents
- Preventing Future Malware Incidents
- Planning For Recovery
- Creating a System Image
- Course Summary
Network Survey & Extraction: Network Analysis
Course: 58 Minutes
- Course Overview
- Network Scanning Tools
- Identifying Network Vulnerabilities
- Alternative Network Vulnerabilities
- Efficient Network Scanning
- Reverse IP Lookup
- Identifying Services
- Operating System Identification
- UDP Scanning
- Stealth Scanning
- Connect Scanning
- Zombie Scanning
- ARP Scanning
- Course Summary
Network Survey & Extraction: Network Monitoring
Course: 52 Minutes
- Course Overview
- Actively Monitoring Services
- Managing Collected Data
- Vulnerability Metrics
- Network Reporting and Record Keeping
- DNS Host Discovery
- Netcat Banner Grabbing
- Tcpdump Connection Filtering
- Tcpdump Protocol Filtering
- Gathering Site Reports
- Firewall Scanning
- SSL/TLS Scanning
- SMTP Scanning
- Course Summary
Defensive CyberOps: Defensive Cyberspace Operations
Course: 43 Minutes
- Course Overview
- Principles of Defensive Cyber Operations
- DCO Measures and Response
- DCO and Cybersecurity
- DCO Maneuver Operations
- DCO Analytics
- DCO Missions
- DCO Operating Domains
- DCO Mission Owner
- DCO Network Owner
- DCO Planning Considerations
- DCO Threat Detection and Characterization
- DCO Tools and Capabilities
- Course Summary
Network & Host Analysis: Protocol Analysis
Course: 58 Minutes
- Course Overview
- Network Data Pattern Analysis
- The Open Systems Interconnection (OSI) Model
- Passive and Active Scanning Approches
- Capturing Traffic Using Wireshark
- Filtering Traffic Using Wireshark
- Customizing Packet Capturing in Wireshark
- Saving and Exporting Captures in Wireshark
- Highlighting Rules Using Wireshark
- Extracting Files Using Wireshark
- Configuring Profiles in Wireshark
- Controlling Filter Display in Wireshark
- Implementing Advanced Filtering in Wireshark
- Course Summary
Network & Host Analysis: Network Protocols
Course: 1 Hour
- Course Overview
- Filtering DNS Traffic
- Filtering TCP Traffic
- Filtering UDP Traffic
- Capturing ICMP Traffic
- Examining HTTP Traffic
- Inspecting SSH Traffic
- Extracting FTP Traffic
- Filtering Email Traffic
- Capturing ARP Traffic
- Capturing DHCP Traffic
- Monitoring Telnet Sessions
- Filtering IPv6 Traffic
- Course Summary
Network & Host Analysis: Network Observations
Course: 1 Hour
- Course Overview
- Displaying Protocol Hierarchies in Wireshark
- Identifying Endpoints Using Wireshark
- Visualizing Networks
- Visualizing Networks in Visio
- Assessing Networks
- Developing Baselines
- Baselining in Wireshark
- Wireshark Capture Engines
- Creating Rules in Wireshark
- Detecting Scans Using Wireshark
- Tunneling Remotely Using Wireshark
- Course Summary
Network & Host Analysis: Network Analysis Formats
Course: 1 Hour
- Course Overview
- NetFlow and IPFIX Collection
- NetFlow and Baselining
- The Benefit of Audit Logs
- Application Access Control
- Tapping Network Traffic
- Emitting and Aggregating Logs
- Queueing Events
- Network Management with SNMP
- Packet Capturing with PCAP
- Whitelisting Applications
- Using Wireshark for Event Detection
- Importing and Exporting PCAP
- Course Summary
Network & Host Analysis: Network Operations
Course: 1 Hour, 1 Minute
- Course Overview
- Network Defense Tools
- Implementing NSM
- SIEM for Threat Activity
- Installing Suricata
- Applying Suricata Rules
- Creating Suricata Alerts
- Generating Suricata Logs
- Installing ELK Stack Prerequisites
- Installing ELK Stack
- Integrating Suricata and ELK Stack
- Navigating Kibana for SIEM
- Integrating Suricata and Wireshark
- Course Summary
Forensic Analysis: Cybercrime Investigations
Course: 1 Hour, 38 Minutes
- Course Overview
- Packet Captures
- Network Forensics
- Capturing Network Traffic
- Working With PCAP Files
- Volatile Data
- Memory Forensics Tools
- Using the Volatility Framework
- Windows Registry
- Locating Evidence Within the Registry
- Registry Analysis Tools
- Categories of Digital Evidence
- Gathering Digital Evidence
- Computer Forensic Analysis Tools
- SANS Investigative Forensic Toolkit (SIFT)
- Analyzing Evidence Using SIFT
- Course Summary
CyberOps Windows Hardening: Windows Server Hardening Best Practices
Course: 1 Hour, 33 Minutes
- Course Overview
- BIOS/UEFI Settings to Improve Workstation Security
- Hardening User Accounts on a Windows Workstation
- Implementing AppLocker Policies on Windows
- Hardening Windows Services and Removing Software
- Patching Windows Systems
- Implementing a Windows Workstation Password Policy
- Implementing a Windows Account Lockout Policy
- Configuring Windows User Rights
- Implementing Full Disk Encryption with BitLocker
- Encrypting USB Drives with BitLocker To Go
- Using Windows Defender as an Antivirus Tool
- Configuring Auditing on a Windows Workstation
- Using Security Templates on a Windows Workstation
- Course Summary
CyberOps Windows Hardening: Windows Workstation Hardening Best Practices
Course: 1 Hour, 30 Minutes
- Course Overview
- BIOS/UEFI Settings to Improve Workstation Security
- Hardening User Accounts on a Windows Workstation
- Implementing AppLocker Policies on Windows
- Hardening Windows Services and Removing Software
- Patching Windows Systems
- Implementing a Windows Workstation Password Policy
- Implementing a Windows Account Lockout Policy
- Configuring Windows User Rights
- Implementing Full Disk Encryption with BitLocker
- Encrypting USB Drives with BitLocker To Go
- Using Windows Defender as an Antivirus Tool
- Configuring Auditing on a Windows Workstation
- Using Security Templates on a Windows Workstation
- Course Summary
Threat Intelligence & Attribution Best Practices: Threat Intelligence Concepts
Course: 1 Hour, 40 Minutes
- Course Overview
- Threat Intelligence
- Key Elements of Threat Intelligence
- The Value of Threat Intelligence
- Using Threat Intelligence
- Cyber Threat Actors
- Common Indicators of Compromise
- Intelligence versus Data versus Information
- Threat Intelligence Lifecycle
- Strategic Threat Intelligence
- Tactical Threat Intelligence
- Operational Threat Intelligence
- Technical Threat Intelligence
- Machine Learning and Threat Intelligence
- Risk Modeling and Threat Intelligence
- Threat Intelligence Use Cases
- The Threat Landscape
- Intrusion Detection and Analysis
- Threat Intelligence Sources
- Course Summary
Assessment: Security Threat Intelligence
Will test your knowledge and application of the topics presented throughout the Security Threat Intelligence courses.
Practice Lab: Security Threat Intelligence (estimated duration: 8 hours)
Perform security threat intelligence tasks such as scanning networks, connecting to remote hosts, scanning websites for vulnerabilities, and using Wireshark to save packet captures. Then perform packet filtering, program verification, scripting and test a service for weaknesses or vulnerabilities.
| Levertijd | Binnen 1 werkdag |
|---|---|
| Online toegang | 365 dagen |
| Lesduur | 23 uur |
| Studiebelasting | Variabel i.v.m. praktijkopdrachten. |
| Leermethoden | Instructie video, Demonstratie video, Knowledge Base |
| Besturingssystemen | Microsoft Windows, Google Chrome OS, Apple MacOS |
| Inbegrepen dienstverlening | Contact met docent per mail en chat, Voortgangsrapportage, 24/7 online toegang |
| Ondersteunde browsers | Internet Explorer, Edge, Firefox, Safari en Chrome |
| MOS Examen | Mogelijk voor bijbehorend examennummer |
| Toegang tot docent | Per mail en chat |
| Extra Opties | Virtual Labs (indien beschikbaar) |
| Aanschaf | Eenmalig bedrag |
Er zijn nog geen reviews geschreven over dit product.
OEM Office Elearning Menu Top 2 in ICT-trainingen 2024!
OEM Office Elearning Menu is trots op de tweede plaats in de categorie ICT-trainingen 2024 bij Beste Opleider van Nederland (Springest/Archipel). Dank aan al onze cursisten voor hun vertrouwen!
Beoordelingen
Er zijn nog geen reviews geschreven over dit product.